Are you concerned about the privacy of your printed documents? You may be surprised to learn that printers have a hidden feature called the Machine Identification Code (MIC) that can track your documents. This code adds a unique watermark to each printed page, allowing the printer to be identified based on the serial number, date, and time of printing. While not all printers utilize this code, many color inkjet and laser printers do, raising questions about privacy and the potential for document traceability.
So, how does the Machine Identification Code work? It is created by printers using a matrix of yellow dots that form an 8×16 format on the page. These dots are nearly invisible to the naked eye but can be detected and analyzed. By deciphering the MIC, the specific printer that was used to create a document can be identified, potentially compromising your privacy.
Key Takeaways:
- Printers have a hidden feature called the Machine Identification Code (MIC) that adds a unique watermark to each printed document.
- The MIC can be used to trace the serial number of the printer and the date and time the document was printed.
- Color inkjet and laser printers are more likely to create the Machine Identification Code.
- Privacy concerns arise from the potential tracking of individuals through their printed documents.
- While it is challenging, there are measures you can take to minimize printer tracking and protect your privacy.
How Does the Machine Identification Code Work?
The Machine Identification Code, also known as MIC, is an integral part of color inkjet and laser printers. This code utilizes a matrix of yellow dots, each measuring approximately 1/10th of a millimeter in diameter, to create a unique watermark on printed documents.
The pattern formed by these yellow dots follows an 8×16 format matrix, occupying a small area on the page. Despite being nearly invisible to the naked eye, these dots encode essential information, including the printer's serial number, as well as the date and time of printing.
“The Machine Identification Code uses a matrix of yellow dots to encode printer details, creating a traceable watermark on printed documents.”
The Machine Identification Code (MIC) allows for the identification of the specific printer that produced a particular document by analyzing the encoded information within the yellow dot pattern.
Understanding the Machine Identification Code
To better grasp the functioning of the Machine Identification Code, let's break it down:
- The MIC is created using a matrix of yellow dots.
- The dots are approximately 1/10th of a millimeter in diameter.
- The dot pattern conforms to an 8×16 format matrix.
- The dots contain the printer's unique serial number.
- The dots also record the date and time the document was printed.
This system enables traceability, allowing forensic experts to connect a specific document to the printer responsible for its production.
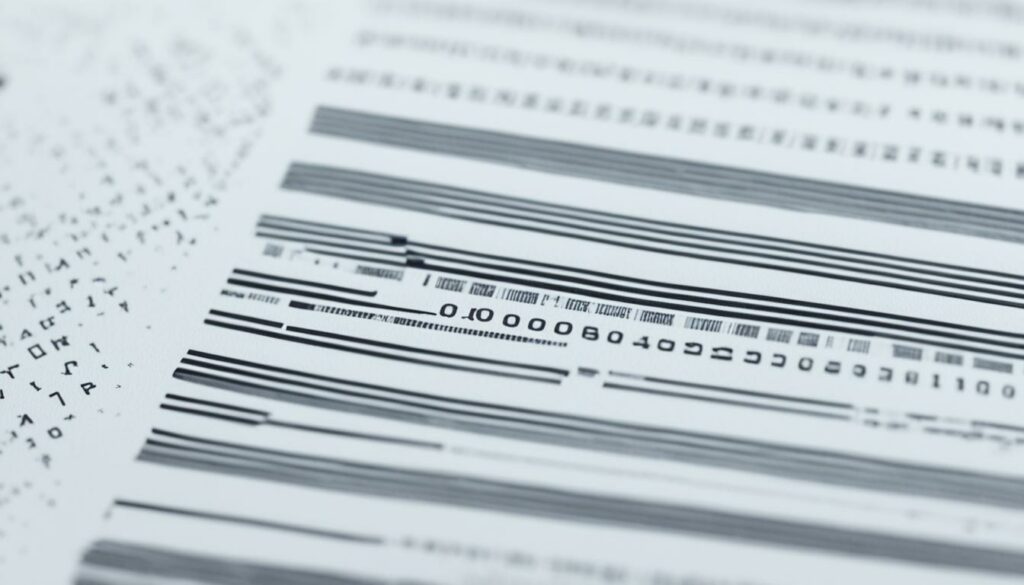
To give you a visual representation of how the Machine Identification Code works, take a look at the image below:
This image visually demonstrates the yellow dot pattern forming the Machine Identification Code. It showcases the intricate matrix and the encoded information it holds, highlighting the functionality and importance of the code in printer traceability.
Advantages of the Machine Identification Code
The Machine Identification Code provides several advantages:
- Enables tracking and identification of the printer used to create a specific document
- Aids in forensic investigations by linking documents to their source
- Promotes traceability and accountability in printing processes
- Aids in counterfeit prevention and detection
In cases where document traceability is crucial, the Machine Identification Code serves as a valuable tool to identify the source printer accurately.
| Advantages of Machine Identification Code |
|---|
| Enables tracking and identification of the printer |
| Aids in forensic investigations |
| Promotes traceability and accountability |
| Aids in counterfeit prevention and detection |
Which Printers Use the Machine Identification Code?
Not all printers use the Machine Identification Code (MIC) to track documents. The MIC is primarily found in color inkjet and laser printers. However, there is no comprehensive list of printers that use this code, making it difficult for individuals to determine if their specific printer generates these traceable codes.
While some printer manufacturers openly advertise the presence of the MIC feature, others do not disclose its existence. This lack of transparency leads to uncertainty and concerns over privacy.
Printer Types Using Machine Identification Code
Printers that commonly use the Machine Identification Code (MIC) for traceability include:
- Color inkjet printers
- Color laser printers
Printer Manufacturers and Transparency
Some printer manufacturers openly acknowledge the presence of the MIC feature and provide information about its usage in their printers. However, other manufacturers do not disclose the existence of the MIC, leaving consumers unaware if their printer is generating these traceable codes.
Printer Manufacturers and MIC Disclosure
| Printer Manufacturer | MIC Disclosure |
|---|---|
| Brand A | Disclosed |
| Brand B | Undisclosed |
| Brand C | Disclosed |
Table: Printer Manufacturers and Their Disclosure of the Machine Identification Code (MIC) feature.

The Concerns About Privacy
The use of the Machine Identification Code raises significant privacy concerns. For individuals who print out flyers expressing their personal or political beliefs, there is a potential risk of being identified through the codes on the printed documents. This raises questions about freedom of speech and the potential for individuals to be tracked and targeted based on their printed materials.
While there is no official comment from the US government on this issue, privacy advocates worry about the potential implications of this technology. The ability to trace documents back to specific printers raises concerns about privacy and the protection of personal information.
| Privacy Concerns | Implications |
|---|---|
| The potential for tracking individuals through printed documents | Risk of targeted surveillance and potential privacy breaches |
| Threats to freedom of speech | Potential censorship and chilling effects on expression |
| Increased vulnerability of personal information | Potential for misuse or unauthorized access to sensitive data |
While some may argue that printer tracking is a necessary measure for security reasons, the concerns about privacy cannot be overlooked. It is essential to strike a balance between security and individual privacy rights in the digital age.

Privacy is a fundamental right that should be protected, and the use of printer tracking technologies raises important ethical and legal questions. Stricter regulations and transparent disclosure about printer tracking practices are necessary to ensure that individuals are aware of the potential risks and can make informed decisions about their privacy.
Real-Life Examples of Printer Tracking
Printer tracking is not just a theoretical concept; there have been real-life instances where it has resulted in the identification of individuals. One notable case involves Reality Winner, an NSA contractor who leaked classified documents pertaining to Russian interference in the 2016 presidential election.
In this particular case, the FBI utilized the hidden watermarks embedded in the printed pages to trace the origin of the leaked documents back to the printer used. The machine identification code revealed crucial information, leading to Winner's subsequent arrest and conviction.
“The FBI announced Monday that it has arrested the woman suspected of leaking a classified document to The Intercept in an effort to further authenticate their findings.” – CNN
Reality Winner's case serves as a concrete example of the consequences printer tracking can have on whistleblowers and individuals who choose to disclose sensitive information. It highlights the potential risks associated with the technology and underscores the need for awareness and privacy protection measures.
Reality Winner: The Whistleblower
In 2017, a document was leaked to online news organization The Intercept, containing classified information about Russian cyber-attacks on U.S. voting systems. The leaked document was traced back to Reality Winner, who was promptly arrested and charged with violating the Espionage Act.
The FBI's investigation into the leak revealed that Winner had printed the document at her workplace using a color laser printer. By analyzing the embedded machine identification code, they were able to link the printed document directly to Winner's specific printer.
Winner's case sparked a public dialogue about printer tracking and the potential implications it has for whistleblowers and those who seek to expose wrongdoing. It serves as a reminder that even seemingly innocuous documents can carry hidden traces that have far-reaching consequences.
Protecting Whistleblowers' Anonymity
The case of Reality Winner highlights the importance of protecting the anonymity of individuals who engage in whistleblowing activities. It raises concerns about the potential chilling effect that printer tracking may have on those who wish to come forward with information.
Efforts are being made to establish safeguards to protect whistleblowers and their privacy. For example, organizations like the Electronic Frontier Foundation (EFF) advocate for the use of tools and techniques that can help mitigate the risks associated with printer tracking.
While printer tracking poses challenges for whistleblowers, it is essential to continue exploring ways to ensure their safety and anonymity. This includes raising awareness about the existence of printer tracking technologies and pushing for stronger legal protections for individuals who expose important information in the public interest.
![]()
Real-life examples such as the case of Reality Winner underscore the need for individuals to be aware of the potential privacy risks associated with printer tracking. It serves as a reminder that seemingly innocuous documents can carry hidden traces and highlights the importance of protecting whistleblowers' anonymity.
Can You Prevent Your Printer from Tracking You?
While it is challenging to completely prevent printer tracking, there are some measures you can take to minimize the risk and protect your privacy. Here are some recommended privacy measures and printer settings:
- Print with black ink only: By using only black ink for your printed documents, you can reduce the traceability potential of the Machine Identification Code (MIC). The MIC is typically generated using color ink, so sticking to black ink limits the visibility of these traceable codes.
- Choose a printer without the Machine Identification Code: Look for printers that do not generate the MIC. Unfortunately, there is no comprehensive list available, but certain printer models are known to not create these traceable codes. Consider doing some research or consulting with experts to find printers without this feature.
- Delete printer's activity logs: Regularly delete the activity logs stored in your printer. These logs may contain information about the documents you've printed, including timestamps, file names, and other metadata. By clearing these logs, you can reduce the amount of potential tracking information associated with your printing history.
- Enable password protection for printer networks: If you use shared printers, secure your printing activities by enabling password protection for the printer network. This prevents unauthorized access to your printing history and helps safeguard your privacy.
By implementing these privacy measures and adjusting your printer settings, you can enhance your privacy and minimize the risk of printer tracking. However, it is important to note that these measures cannot completely eliminate the potential for traceability. The invisible yellow dots generated by the MIC will still be present on the printed documents.
| Privacy Measures | Effectiveness |
|---|---|
| Printing with black ink only | Reduces traceability potential of MIC |
| Choosing a printer without MIC | Eliminates MIC generation |
| Deleting printer's activity logs | Minimizes potential tracking information |
| Enabling password protection for printer networks | Secures printing activities on shared printers |
Note: These privacy measures are effective to some extent but cannot guarantee complete prevention of printer tracking. The presence of the Machine Identification Code remains a challenge to overcome in ensuring absolute privacy.
![]()
“Protecting your privacy while using a printer requires taking proactive steps to minimize the risk of tracking. By implementing recommended privacy measures and adjusting your printer settings, you can better safeguard your personal information and maintain control over your printed documents.”
Tips for Disposing of an Old Printer
When it's time to say goodbye to your old printer, it's important to take steps to protect your privacy and ensure that any sensitive data stored in the printer's memory is completely wiped. Here are some tips to help you dispose of your old printer securely:
-
Unplug and Check: Start by unplugging the printer from the power source. Then, plug it back in and check if any saved data or settings are still present. Sometimes, printers retain information even after being unplugged, so it's essential to verify that all data has been erased.
-
Reset and Clear: For wireless printers, manually resetting the printer's settings can help remove any traces of past usage. Look for a “Reset to Factory Defaults” option in the printer's menu settings and follow the instructions to reset the device. Additionally, clearing all Wi-Fi connections will further ensure that no personal information remains on the printer.
-
Wipe Printer Memory: Some printers have a built-in option to wipe the memory or hard drive. Check the printer's manual or manufacturer's website for instructions on how to perform a secure memory wipe. This process will overwrite any stored data, making it virtually impossible to retrieve.
-
Physical Destruction: If you have concerns about data security and want to take extra precautions, you can physically destroy the printer. Remove any removable memory cards or hard drives, and then use a hammer or other heavy object to crush the printer's internal components. This ensures that any data stored on the device is completely obliterated.
By following these tips, you can protect your privacy and prevent any potential data breaches when disposing of an old printer.
“Safely disposing of an old printer is crucial for protecting your privacy and ensuring that any sensitive information does not end up in the wrong hands.” – Privacy Expert

| Disposal Method | Level of Data Security |
|---|---|
| Unplug and Check | Low |
| Reset and Clear | Moderate |
| Wipe Printer Memory | High |
| Physical Destruction | Extreme |
The Limitations of Privacy Protection
While taking proactive steps to protect your privacy when using printers can reduce the amount of potential metadata stored, it is important to recognize the limitations. Even if you delete activity logs and wipe printer memory, the Machine Identification Code, represented by the invisible yellow dots, cannot be erased. This means that any printed document could potentially be traced back to the specific printer and potentially to the individual who printed it. When dealing with sensitive information, it is advisable to opt for alternative means of communication, such as pen and paper.
![]()
“We must be cautious when relying solely on printer privacy settings, as the Machine Identification Code remains an invisible trace. While measures can be taken to minimize tracking, it is crucial to remember that ultimately, printers can leave behind information that compromises privacy.”
– Privacy Advocate
History and Development of Printer Tracking
Printer tracking, through the use of the Machine Identification Code (MIC), has a long history dating back to the mid-1980s. It was Xerox that pioneered this encoding mechanism, aiming to combat counterfeiting by adding unique identifying marks to each printed page. The MIC, also known as watermarking technology, consists of a series of nearly invisible yellow dots that form a unique pattern on printed documents.
While the existence of the MIC on printers was not widely known until 2004, it was the Electronic Frontier Foundation (EFF) that played a crucial role in decoding and raising awareness about these hidden codes. In their research, the EFF discovered that all major manufacturers of color laser printers had been involved in a secret agreement to enable forensic traceability of printed output, which ignited a public debate surrounding the privacy implications of printer tracking.
The Significance of the Machine Identification Code
Each printer has a unique MIC pattern that contains information such as the printer's serial number, the date and time of printing, and other printer-specific details. These microscopic yellow dots are embedded throughout the document and can only be detected and analyzed under certain lighting or using image-processing software. This technology allows for the identification of the specific printer used to create a document, providing a form of traceability that raises concerns about privacy and anonymity.
The Role of Watermarking Technology in Forensics
Watermarking technology, in the context of printer tracking, serves as a valuable tool for forensic investigations. By analyzing the MIC, law enforcement agencies and other entities can trace printed documents back to their source printer, helping to identify potential suspects or verify the authenticity of critical documents. While this technology has proven to be useful in certain investigations, it also raises important questions about the balance between privacy rights and the need for security.
Overall, the history and development of printer tracking, driven by the Machine Identification Code and watermarking technology, have sparked ongoing discussions about privacy, surveillance, and individual rights. As technology continues to advance, it is essential for individuals and society as a whole to critically evaluate the implications of such tracking mechanisms and ensure that privacy concerns are adequately addressed.
Visibility of Machine Identification Code
The Machine Identification Code (MIC), represented by the yellow dots, can be made visible through various detection methods. By scanning and enhancing a printed page's yellow channel using image processing software, the pattern of yellow dots becomes apparent. Under good lighting conditions or with the help of a magnifying glass, users can observe the hidden watermark on their printed documents.
However, one of the most effective methods to reveal the MIC is by using UV-light. When exposed to UV-light, the yellow dots become clearly recognizable, allowing for easy identification and analysis of the traceable codes encoded on printed pages.
Understanding the visibility of the Machine Identification Code serves as a reminder of the need for privacy protection measures. By being aware of the presence of the code and taking necessary precautions, individuals can better safeguard their privacy when printing sensitive documents.
Conclusion
Printer tracking through the Machine Identification Code has significant privacy implications. The ability to trace documents back to specific printers raises concerns about freedom of speech, anonymity, and the potential for targeted surveillance. While it is challenging to entirely prevent printer tracking, individuals can take steps to protect their privacy when using printers.
However, it is important to recognize the limitations of privacy protection. The invisible yellow dots, representing the Machine Identification Code, cannot be erased, making it possible to trace printed documents back to the specific printer. This highlights the need for ongoing discussions about privacy rights and responsibilities in the digital age.
The ongoing development and use of printer tracking technology call for increased awareness and vigilance in safeguarding personal information. As individuals, it is crucial to stay informed about the features and functionalities of our printers to make informed decisions. Balancing the convenience of modern printing technology with the preservation of privacy is a delicate task that requires continuous evaluation and exploration of privacy-enhancing measures.

I'm Morgan, the creator of VPNForMe — a site born from too many hours spent side-eyeing sketchy VPN reviews and buffering videos.
I wanted a place where people could get straight answers about privacy, streaming access, and which VPNs actually deliver — without the hype or tech jargon.

